WIth Synology, Docker, Portainer, a Guacamole image and some know-how, you too can access your home network from abroad
Tag: IT
Docker Desktop – Restoring a WordPress Site
Restore a wordpress site with Docker in a safe, hosted Synology environment.
Synology DS420+ review
Review of the Synology DS420+
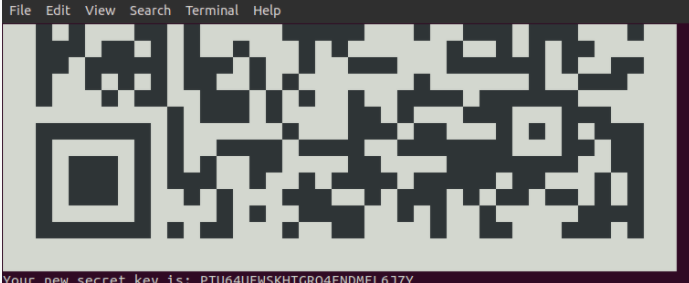
Ubuntu – Add Google 2FA for SSH
The Setup Host: Ubuntu 18.04 “Bionic Beaver” releaseSoftware: Google Chrome Original article found on linuxbabe Super handy, and secure way to ssh into your Linux Box at home. This uses the Android Google Authenticator for the QR code, generated right
Read More
Ubuntu Chrome Remote Desktop configuration
The Setup Host: Ubuntu 18.04 “Bionic Beaver” releaseSoftware: Google Chrome I thought this was weird: I couldn’t actually download the Chrome browser. Couldn’t do it from firefox (the Ubuntu default), or chromium (the open-source O.G Chrome package). I thought that
Read More
Oracle VirtualBox – Configure Guest-VM network to communicate with Host network
This is going to focus on configuring an Oracle Virtualbox VM to do a few things:-make it so the host, and local host network can see, ping, remote and use fileshares to the Oracle Box guest VM-Enable the Oracle box
Read More
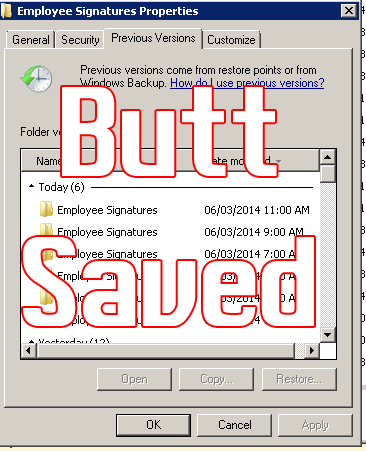
GPO enable VSS in Win 7
Volume Shadow copy has saved my butt on file, exchange, and SQL servers. Typically, IT departments discourage previous versions on desktops mainly because it opens up issues with disk space and if it’s really worth saving or rescuing an MP3
Read More
GPO add corporate picture to your AD logon account
Group Policy to set default Windows 7 Account pictures.
Configuring NPS on Server 2012 with Cisco WLC: Part 2
In part 1 of this tutorial, I stepped through configuration of the Cisco Equipment and configuration of the Network Policy Server with Certificate. In this tutorial, I’ll show you how to tie it all up in Group Policy. This tutorial
Read More
Configuring NPS on Server 2012 with Cisco WLC: Part 1
This How-to article is meant to configure Windows Server 2012 Network Policy Server, Certificate Authority with a Cisco WLC 2504 series (with Software version 7.4.100.0) As specific as that list is, much of what Cisco offers with older IOS versions still holds true.
Read More